How Blockchain Investigators Track Bitcoin Ethereum and USDT
How Blockchain Investigators Track Bitcoin Ethereum and USDT
In 2026, the digital asset landscape has entered what analysts call the “Great Normalization.” With stablecoins like USDT serving as the new rails for institutional finance, the sophistication of financial crime has escalated, making blockchain forensics an essential pillar of global security.
To understand how experts trace stolen cryptocurrency, we must look at the convergence of on-chain analytics, AI-driven intelligence, and military-grade digital forensics blockchain protocols. This article explores the methodologies used to track cryptocurrency transactions in real time and dismantle the complex networks of modern cybercrime.
The Mechanics of 2026 Blockchain Forensics: How Investigators Trace Bitcoin Ethereum and USDT
1. Establishing the Anchor: The Start of a Crypto Forensic Analysis
Every blockchain forensic investigation begins with an “anchor point”—a known data fragment such as a victim’s wallet address tracking result or a specific transaction hash. In a crypto scam investigation, this anchor allows investigators to initiate crypto transaction tracing to see exactly where the initial “leak” of capital occurred.
Using an enterprise blockchain analytics suite, investigators perform a preliminary blockchain explorer analysis. This process isn’t just about looking at a ledger; it involves blockchain data analysis platform tools that can ingest millions of data points to provide a clean transaction graph analysis.
2. Advanced Techniques in Cryptocurrency Forensics
Once the anchor is set, cryptocurrency forensics experts deploy several high-level heuristics to pierce the veil of pseudonymity.
-
Wallet Clustering Analysis: By using wallet clustering analysis, investigators can group thousands of seemingly unrelated addresses under a single “Entity.” This is crucial for bitcoin transaction tracing, where a single hacker might use a “peeling chain” to move small amounts of BTC to avoid detection.
-
Behavioral Pattern Recognition: Modern blockchain analytics tools use machine learning to identify “Agentic AI” signatures—autonomous bots used by syndicates to wash funds. Crypto intelligence analysis helps distinguish between a human user and an automated laundering script.
-
Cross-Chain “Hop” Tracing: In 2026, ethereum transaction tracing often involves tracking funds as they move through bridges to other chains. Blockchain tracing tools now provide “automatic route identification” to follow the money across 50+ incompatible blockchains simultaneously.
3. Tracing the "Big Three": Bitcoin, Ethereum, and USDT
Each asset requires a unique blockchain cyber investigation strategy:
-
Bitcoin Transaction Tracing: Focused on UTXO (Unspent Transaction Output) models. Experts use bitcoin forensic tools to follow the “change” in transactions, identifying the true destination of the stolen capital.
-
Ethereum Transaction Tracing: Because Ethereum is account-based and smart-contract heavy, investigators use DeFi transaction monitoring to track funds moving through decentralized exchanges (DEXs) and liquidity pools.
-
Trace USDT Transaction: Since USDT exists on multiple chains (TRON, Ethereum, etc.), blockchain fraud tracing must account for “bridge swaps.” Investigators work with crypto compliance monitoring teams to flag these transactions at the exchange level.
4. The Toolkit of a Blockchain Cybercrime Investigation
To stay ahead of criminals, firms must utilize a robust stack of blockchain intelligence tools.
| Tool Category | Purpose | Examples |
| Forensic Blockchain Tools | Deep-dive evidence packaging for court. | Cyberh4cks Military Grade, Bitreclaim Forensics |
| Blockchain Analytics Platform | High-level risk scoring and compliance. | Elliptic, Crystal Blockchain |
| Blockchain Security Analytics | Real-time threat hunting and monitoring. | AnChain, Nansen |
| Crypto Investigation Tools | OSINT and attribution mapping. | Maltego, Breadcrumbs |
5. Real-Time Monitoring and AML Blockchain Analysis
In the 2026 regulatory environment—shaped by the U.S. GENIUS Act and the EU’s MiCA—AML blockchain analysis is no longer reactive; it is proactive. Crypto transaction monitoring systems now provide real-time alerts when a wallet address investigation links a user to a sanctioned entity or a crypto money laundering tracing pattern.
Blockchain compliance monitoring ensures that Virtual Asset Service Providers (VASPs) can immediately freeze assets. This is the core of blockchain fraud detection: identifying the “Cash-Out” point before the thief can convert the digital asset into fiat currency.
6. Crypto Scam Recovery Investigation: Can Stolen Funds Be Retrieved?
A common question remains: can bitcoin transactions be traced to the point of recovery? The answer is a qualified “yes.” While the blockchain is immutable, the “off-ramps” (exchanges) are regulated.
A crypto scam recovery investigation follows a strict blockchain evidence collection lifecycle:
-
Identification: Identifying the how investigators trace bitcoin transactions via the ledger.
-
Preservation: Generating cryptographic hashes of the evidence to ensure it is court-admissible.
-
Attribution: Linking the wallet address tracking data to a real-world identity through OSINT and exchange subpoenas.
-
Intervention: Using blockchain risk analysis to convince an exchange to freeze the target wallet.
7. Conclusion: The Future of Digital Forensics Blockchain
As we look toward the end of 2026, blockchain intelligence analysis will only become more integrated into the global financial system. Whether you are a corporation looking for crypto forensic investigation services or a victim trying to trace stolen bitcoin, the key lies in speed and technical pedigree.
Understanding how to track crypto wallet transactions and how to trace stolen cryptocurrency is no longer just a niche skill—it is a requirement for the “Great Normalization” of the digital age.




3 Comments
Don’t invest with Plus500
Beware of Plus500
Plus500 is a complete ruse they blocked me on twitter after confronting them.
Please be aware that the people behind Plus500 are con artists, my so-called appointed advisor, was pushing pressure on me to borrow money ($495K) to fund my Plus account so that I could make more money. I mistook the company for a legitimate one, but their are a con artist. I was initially told that the minimum deposit for trading with them was US$40000, which I did. He continued to pressurize me to put more money in. I saw that the online address he was using to trade my money was a demo by the time I investigated it . Since I refuse to go and borrow more money, he refused to call me again. I contacted American forensic firm cyberh4cks. They consulted with me and create a strategy for confronting them. They set in motion the process to retrieve my funds using the latest Cyber tools, open source intelligence (OSINT),cyber investigation and triangulation. Which was successful
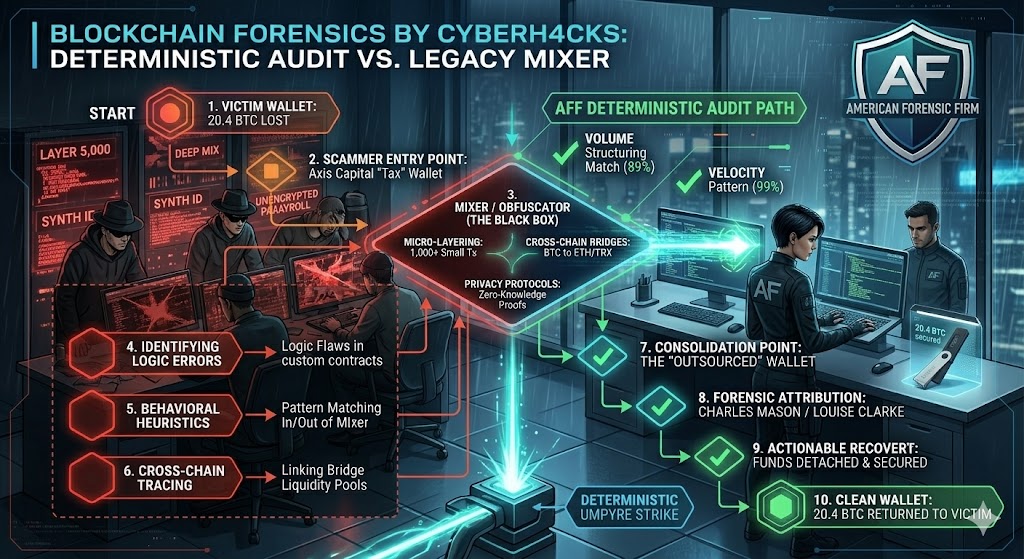
Axis Capital contacted me last year through a very British sounding “Jonathon Higgins” about investing in a firm named Belgrave Resources, which was a genuine Canadian oil exploration company that you could look up. However, while they were considering listing, they had not yet listed, and after writing them, I discovered that this company and its workers are engaged in large-scale scamming. Axis Capital’s primary participants are Canadian Charles Mason, British Jonathan Phelps, and British Louise Clarke. In Australian dollars, I lost $3.1 million. I opened a case with blockchain forensics with cyberh4cks as soon as I understood what had transpired to help reclaim my losses.
Reliable Stolen Fund Recovery Experts Contact near me is cyberh4cks
I recently had my Ethereum and non-fungible tokens stolen. I visited a fake investment website and my funds were gone. They were worth fifty thousand dollars, completely lost. I wasn’t having that. I checked across the net for some dependable stolen fund recovery experts to see if they could retrieve the funds. That’s when I came upon a forum, I think Quora where there was several confessions of American Forensic firm cyberh4cks doing digital triangulation from the outsourced website called MicroStrategy and NovatechFX. It was a gifting website similar to what I had involved myself with. Well, I logged onto their website and wrote to them about my funds recovery request. They were simply amazing! They worked on my case in matter of days recouping everything back to my wallet. I’m full of praise for this teams smart contract audit trace from the outsourced wallets. Their email support@cyberh4cks.com might come in handy for quick communication and documentation of. I would ask anyone swindled by individuals or websites and have their funds lost, there’s an easy solution and that would be smart contract audit with cyberh4cks, as this was the only thing that saved me. They indeed are professionals.